SlashNext Blog
Phishing, social engineering, and modern threats.
Featured Article
Think Security Training Will Save You From Phishing Attacks? Think Again!
What’s Required: Intercept phishing attempts before they reach the intended targets In the vast and intricate web of cybersecurity threats, phishing attacks stand out for their deceptively simple yet alarmingly effective tactics. As we delve into the anatomy of a typical phishing scam, it becomes apparent why these attacks not only persist but thrive in […]
Featured Article
10 Ways URL Analysis & Enrichment Can Help Ease Your SOC’s Challenges in 2020
On-demand phishing URL analysis solutions can help ease your SOC teams’ pain and challenges.
Blog Subscription

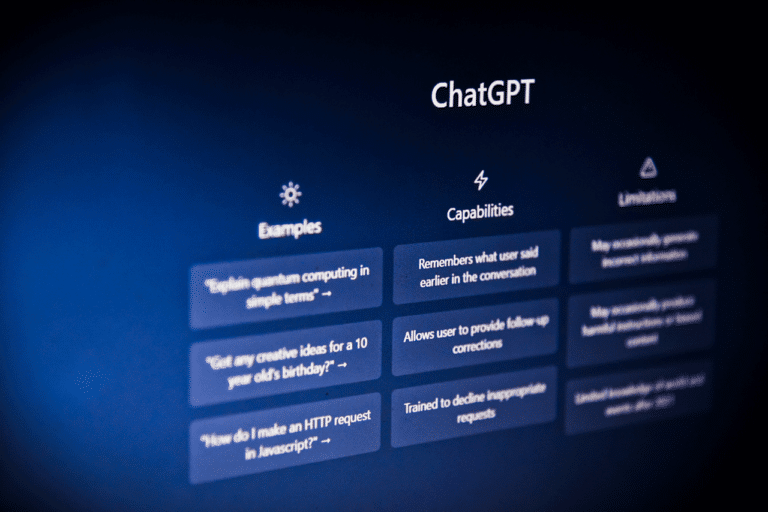
Today’s cybersecurity health checks must identify AI based threats. Does yours?
Your organization will…

Listen to These Recordings: Deepfake Social Engineering Scams Are Scaring Victims
Deepfake social engine…

Mobile Threats Increase as Hackers Exploit the Lack of BYOD Security
The rising trend of em…

G2 Places SlashNext in Top 3 for Integrated Cloud Email Security for 2023, #1 Ratings in Many Cat...
SlashNext has been nam…

Five Types of Business Email Compromise Attacks and How to Prevent Them
In a recent blog, we c…

Latest FBI IC3 Report Reveals BEC and Crypto Scams Top the List of the $10.3 Billion Losses in 2022
The Federal Bureau of …

The Downside to March Madness – a Busted Bracket and a Data Breach
Back in the 1930s, Mar…

SlashNext Expands Collaboration with Microsoft Intelligent Security Association (MISA) Membership
We are excited to expa…
It’s Time to Get Started with SlashNext
Learn how to leverage the industry’s best zero-hour phishing protection in your environment.
6701 Koll Center Parkway, Suite 250
Pleasanton CA 94566
800.930.8643
info@slashnext.com
© All Rights Reserved, SlashNext, Inc.