Weaponized Documents: It’s Just a Matter of Time Before One is Opened
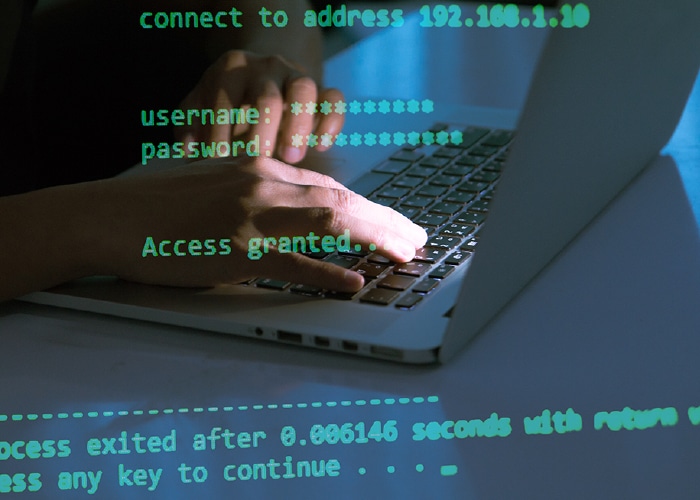
Weaponized documents are delivered via legitimate looking emails. PDFs, Excel or Word documents are attached to these emails and contain links to malware or phishing sites that compromise a system or network.