SEER™ Threat Detection Technology
Patented behavioral phishing detection and machine learning to detect unknown threats with unmatched accuracy.
Detect More Evasive Threats
SlashNext’s patented SEER™ technology brings cloud-scale resources to real-time, multi-vector, multi-payload phishing threat detection. The SEER approach sees through more evasion tactics and detects previously unknown, zero-hour threats missed by URL inspection and domain reputation analysis methods.
SEER technology addresses:
- Phishing and social engineering payloads beyond fake login pages
- Shortened links
- Multiple URL redirects / forwards
- Other types of URL obfuscation
- Multi-stage attacks requiring user interaction, even captchas
- Use of compromised websites and legitimate hosting infrastructure
Stop The Email Attacks That Impact Your Business
Credential Stealing
The act of attaining passwords with the intent of accessing protected data.
Spear Phishing
Targeted attack to gain access to an individual’s account or impersonate a specific individual
SMiShing
Using text messages to trick users into divulging passwords or other PII for fraudulent use.
Social Engineering
Using deception to manipulate users into divulging confidential information for fraudulent use.
BEC, ATO and Supply Chain Attacks
Targets executives or financial teams to defraud a company for financial gain.
Trusted Services Compromise
Commonly used to launch phishing attacks or hack other trusted domains.
Rogueware and
HTML Attachments
Bank and Payment Fraud
Social engineering tactics to obtain money, assets or other property held by an organization.
Global Cloud and In-Channel Detection with SEER™
SEER (Session Emulation and Environment Reconnaissance) uses a unique combination of techniques to see through evasion tactics and accurately detect phishing pages, even those on compromised websites and legitimate infrastructure. A broad intelligence gathering network and more powerful detection technology result in over 10K new detections daily, with thousands not available anywhere else.
The SlashNext Advantage is Your Advantage
Preemptive
Global, proactive threat hunting provides advance visibility, detection, and protection from emerging threats
Real-Time
Real-time, automated detection provides more effective protection from zero-hour threats
Extreme Accuracy
Near-zero false positives results in immediately actionable, block-ready threat intelligence
Overcomes Evasion Tactics
Detects threats missed by URL inspection and domain reputation analysis methods
Multi-Vector, Multi-Payload
Covers more types of phishing and social engineering payloads across all phishing attack vectors, not just email
Deployment Flexibility
Deploy to mobile, endpoints, and existing tools and infrastructure
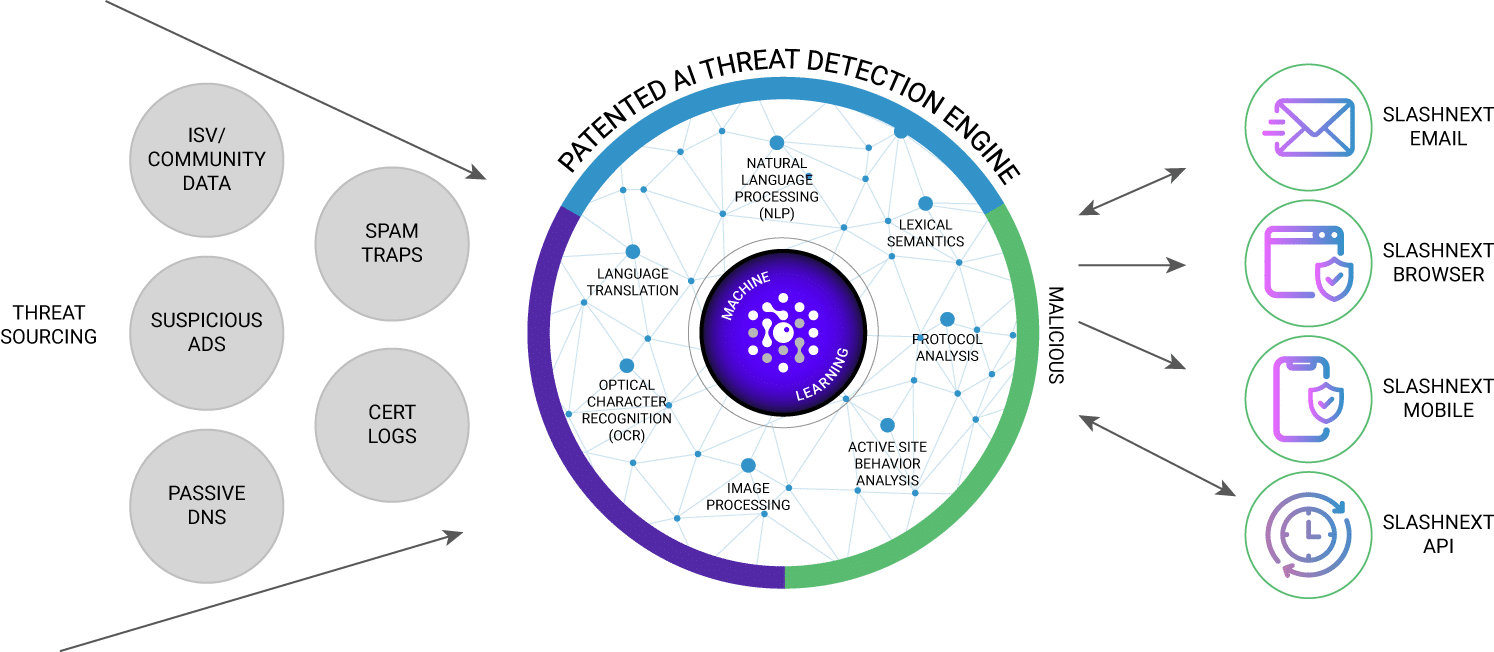
Global, Multi-Vector Threat Sourcing
SlashNext SEER™ technology leverages a global, multi-vector threat intelligence network to proactively source suspicious URLs.
This network includes:
- Global hardware sensors inspecting billions of daily Internet transactions in real-time
- Spam traps
- Suspicious ad networks
- Passive DNS sensors
- Real-time certificate transparency logs
Deployment Flexibility
SlashNext SEER technology powers all SlashNext anti-phishing products, providing a new layer of real-time, multi-vector, multi-payload phishing protection across mobile devices, desktops, and network controls.
Integrations with leading TIP, SIEM, SOAR, DNS, NGFW, and MDM/EMM products enable rapid integration and deployment with existing tools and infrastructure. SlashNext technology can also be accessed on-demand for large-scale, automated phishing URL analysis, phishing IR, and threat hunting.
Extreme Accuracy
Patented SEER technology uses virtual browsers in a purpose-built cloud to perform dynamic, run-time analysis of suspicious web pages. Together with mature machine learning algorithms, SEER delivers binary verdicts—not threat scores—with 99.07% precision.
This uniquely effective approach uses:
- Virtual browsers to dynamically load webpage contents and analyze site behavior
- Natural Language Processing (NLP) and computer vision techniques to understand the textual and visual context of a rendered webpage
- Dynamic site behavioral analysis (fill out forms, analyze behavior, follow re-directs, etc.)
- Mature machine learning algorithms deliver accurate, binary verdicts rather than threat scores
Our Latest SlashNext Blog Posts

From Caesar to Cyberspace: The Growing Menace of Obfuscated Phishing Scams
In the world of cybersecurity, it often feels like we’re revisiting familiar problems, albeit with a modern twist. The essence of the issue isn’t about

Think Security Training Will Save You From Phishing Attacks? Think Again!
What’s Required: Intercept phishing attempts before they reach the intended targets In the vast and intricate web of cybersecurity threats, phishing attacks stand out for

Evolving Cyber Threats: Insights and Strategies from the 2023 FBI IC3 Report
Latest FBI IC3 Report shows a record year for cybercrime: record-setting $12.5 billion in losses The 2023 FBI IC3 report reveals not just numbers but
Experience SlashNext Protection in Action
Request a free trial to see how SlashNext detects zero-hour threats in real-time and stop the attacks that impact your business.
6701 Koll Center Parkway, Suite 250
Pleasanton CA 94566
800.930.8643
info@slashnext.com
© All Rights Reserved, SlashNext, Inc.


